[UPDATE] A couple days after I declared success on this project, the village piece stopped lighting up even when I put batteries back in it. If any of you electrical wizards out there can tell me what I did wrong, I would love to know. Or maybe it’s just some crazy coincidence that both bulbs burned out at the same time mere days after I changed the power source. Occam’s Razor disagrees with that theory. I’ve left the post as it was originally written so you can debug it for me (and laugh at my feeling of success.)
Tyla always sets up our Thomas Kinkaide Christmas village as part of the decorations. Just about every piece has a plug so it all goes into a power strip which, this year, we can control with a remote. But there were two pieces that ran on batteries and thus had separate switches. This year I set out to convert them to use power from the wall just like the rest of the pieces.
The first piece I tried were the street lights. They took two batteries. I purchased an adjustable power adapter, set it to 3V, touched the wires to the right places and POOF. I blew out the lights. I still don’t know what happened because I had tried quite a few things before I realized the lights were broken, but I think I might have hooked up the power while the batteries were also inserted resulting in 6 volts to the lights. Oops. I immediately went online and purchased replacement streetlights. They’re from a different village set but look fine in our set. This new set was sold with a power adapter so I had no problems there.
The second village piece was a little skating rink. Now it should be noted that there’s only one place to buy pieces for this village set (The Bradford Exchange.) They’re extremely annoying to deal with. Anything you order takes at least a month to arrive, most pieces are limited editions, and you often have to sign up for a set of pieces that arrive installments just to get the one you want. The net effect is that if destroyed this village piece, there was pretty much no way to replace it. I was appropriately nervous given the broken streetlights staring at me from the trash can.
I measured the voltage of the adjustable wall wart and even though I had it set to 3V, it said 3.2V. For most projects, I would have just tried that to see if it worked, but I decided to learn something new and build a circuit to knock the voltage down to something more like 2.6 or 2.7V which is what two lightly used AAs would produce.
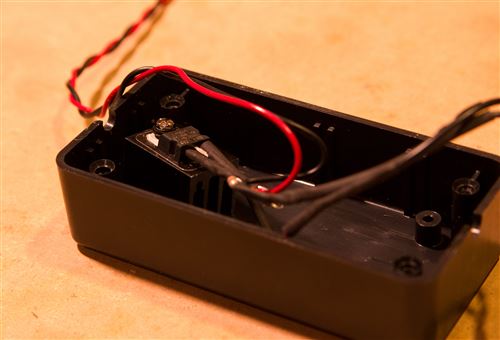
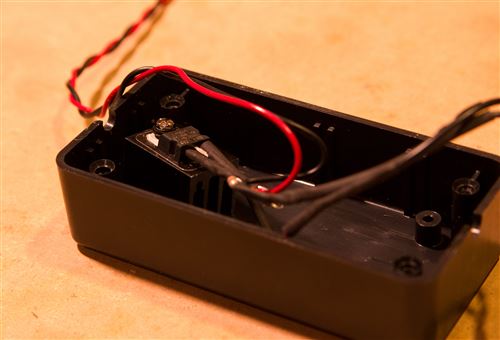
To that end, I purchased an LM317 adjustable voltage regular and dug out the rest of my electronics parts. After watching some YouTube videos and lots of trial and error, I ended up with a simple circuit that spit out 2.72V. Perfect!

The next task was to transfer this off the breadboard and solder the connections. I made everything nice and neat with shrink wrap and a small box to hold the voltage regular and it’s heat sink. (I added a heat sink after taking the picture above.) I used red and black wires to help me remember positive and negative voltage, but it dawned on me later that I should have used white so it was easier to hide under the fake snow. The wire was twisted using a trick I learned from Ben Heck: clamp down the wires on one end and stick the other ends in your power drill. Voila! I also added a plug near the village piece for easy setup, takedown and storage.

The last piece of the puzzle was connecting the wires to the terminals where the batteries would normally go. I could have soldered them on, but I was trying to modify the village piece as little as possible. So instead of anything permanent, I created wooden batteries! I cut 1/2” dowels, drilled pilot holes in each end, and attached screws. The first battery got the positive and negative leads from the plug attached to its ends. The second battery just has a wire running between the two ends to transfer the power. Now I have removable “batteries” and I suppose I could use this same setup to power other 3V battery devices.

It was pretty nerve-wracking the first time I tried it (after measuring the voltage a hundred times), but everything works! I was able to turn the wall wart down to 4.5V and still get 2.7V out of the voltage regulator. The heat sink is doing it’s job and the box has a very tiny bit of extra warmth but nothing anywhere near dangerous. Here’s what the finished product looks like with the light inside the cocoa stand and the large pine tree:

If we get any more battery powered pieces, I should be able to add a couple more leads off of this same voltage regulator, make some more wooden batteries, and be done pretty quickly.
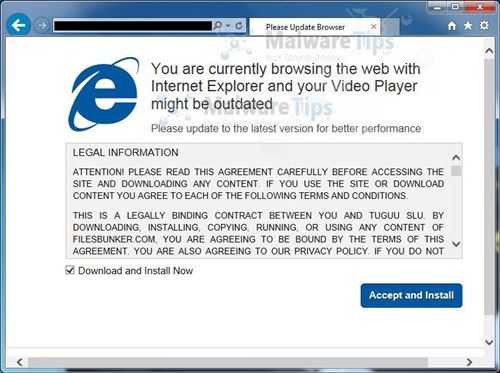
 So now you’ve failed Part 1 or Part 2 of this security series and you have a virus. What should you do? The best thing is to stop everything. Turn off the machine and call your favorite geek. Offer them cookies and ask nicely. Remember that the virus warning might be fake and there’s nothing wrong with your computer.
So now you’ve failed Part 1 or Part 2 of this security series and you have a virus. What should you do? The best thing is to stop everything. Turn off the machine and call your favorite geek. Offer them cookies and ask nicely. Remember that the virus warning might be fake and there’s nothing wrong with your computer.

 My project at work is called Power Query for Excel. We released our first version last summer and now our second version is available as part of a larger offering called “Power BI for Office 365.” BI stands for Business Intelligence. The offering includes a bunch of tools that help you make sense of your data, create nice reports and then share them out with your colleagues. This marks the first time that something I’ve worked on at Microsoft is available for purchase!
My project at work is called Power Query for Excel. We released our first version last summer and now our second version is available as part of a larger offering called “Power BI for Office 365.” BI stands for Business Intelligence. The offering includes a bunch of tools that help you make sense of your data, create nice reports and then share them out with your colleagues. This marks the first time that something I’ve worked on at Microsoft is available for purchase! I don’t know about you, but I’m an email packrat. Steve Gibson, the security genius behind
I don’t know about you, but I’m an email packrat. Steve Gibson, the security genius behind 



 It had been a while since I rebuilt my computer so I decided to do it over Thanksgiving break. I was amazed at how quickly it went! Windows 8.1 installed off a USB key in the blink of an eye. I probably could have used the reset functionality built into Windows 8 but I really wanted to do a bare bones completely clean install. Windows 8.1 remembers pretty much every customization I did to the machine and even all of the apps that I had downloaded from the Windows Store. Office and a few other desktop apps required manual install, but Office 2013 is takes literally a couple minutes to install.
It had been a while since I rebuilt my computer so I decided to do it over Thanksgiving break. I was amazed at how quickly it went! Windows 8.1 installed off a USB key in the blink of an eye. I probably could have used the reset functionality built into Windows 8 but I really wanted to do a bare bones completely clean install. Windows 8.1 remembers pretty much every customization I did to the machine and even all of the apps that I had downloaded from the Windows Store. Office and a few other desktop apps required manual install, but Office 2013 is takes literally a couple minutes to install. I have about a dozen Windows Phone and Windows 8 Store apps. They’re all paid apps, mostly because I’m too lazy to mess around with advertising and it’s nice to get a little money, even if it’s just a few bucks, for my hobby.
I have about a dozen Windows Phone and Windows 8 Store apps. They’re all paid apps, mostly because I’m too lazy to mess around with advertising and it’s nice to get a little money, even if it’s just a few bucks, for my hobby.